The digital banking landscape in 2026 is marked by a shift from broad attacks to highly targeted psychological warfare. As financial institutions harden their technical perimeters, criminals have pivoted toward the most reliable vulnerability which is human judgment.
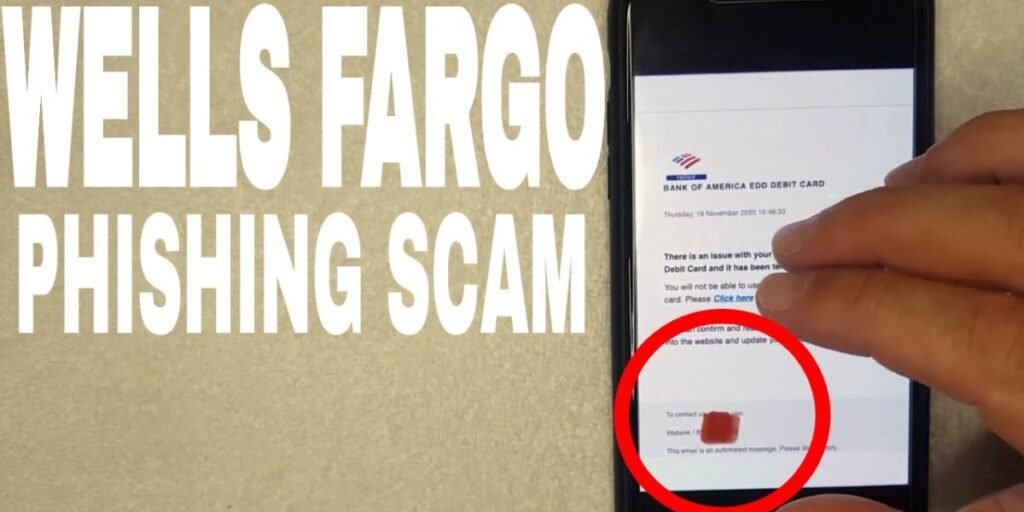
Wells Fargo phishing social engineering is a method of theft where attackers use a combination of fake alerts and emotional pressure to bypass multi-factor authentication. These operations are not random but follow a specific protocol designed to trick you into handing over your One-Time Passcode (OTP) or login credentials.
For any Wells Fargo customer, the ability to distinguish a genuine bank notification from a sophisticated fake is the only way to protect their capital from total loss.
About Wells Fargo
Wells Fargo and Company was founded on March 18, 1852, by Henry Wells and William G. Fargo. Originally established in San Francisco to provide banking and express delivery services during the California Gold Rush, the company is now headquartered in San Francisco, California. It operates as one of the largest financial services companies in the world, managing nearly $1.9 trillion in assets and serving one in three American households.
The bank provides a massive variety of financial products across multiple divisions. Its retail banking sector handles personal checking, savings, and debit cards, while the consumer lending branch manages mortgages, auto loans, and student loans.
For higher-level financial needs, the bank offers wealth and investment management, brokerage services through Wells Fargo Advisors, and commercial banking for small businesses and large corporations.
This massive footprint across the USA and global markets makes it a high-yield target for automated scam campaigns because a single wave of fraudulent messages has a high probability of reaching a real account holder.
What Wells Fargo Phishing and Social Engineering Really Means
In the context of modern cybercrime, these two terms work in tandem to steal your money.
- Phishing: This is the delivery vehicle. It includes the email, the text (smishing), or the phone call (vishing) that contains the malicious payload or link.
- Social Engineering: This is the weaponized psychology behind the message. It uses principles like authority, urgency, and scarcity to make you act without thinking.
Instead of trying to hack into Wells Fargo servers, a scammer hacks the customer. They might impersonate a Wells Fargo fraud investigator who sounds professional and helpful, using a spoofed caller ID to make the call appear as if it is coming from a legitimate 1-800 number.
Their objective is to create a synthetic crisis that forces you to act before you think. They are not just looking for your password, they want your One-Time Passcode (OTP) or your session token that allows them to move money via Zelle or wire transfer in minutes.
Why Scammers Target Wells Fargo
The volume of customers is the primary driver. If an attacker sends out 100,000 automated texts, the mathematical probability of hitting a real Wells Fargo account holder is extremely high.
Furthermore, the bank’s legitimate use of short codes for security alerts, such as 93557 or 93733, creates a baseline of trust that scammers exploit by using similar-looking long-form numbers or hijacked short-code gateways to send wells fargo scams notifications.
How Wells Fargo Scams Typically Work
The execution of these attacks is often clinical, following a specific kill chain designed to end in an unauthorized transfer of funds.
Fake emails, texts, or calls
The initial contact is unsolicited and designed to look routine. Now, AI-driven bots can generate unique wells fargo phishing email variations that have perfect grammar and use the victim’s actual name, likely harvested from third-party data breaches.
Additionally, Phone calls now frequently use AI voice cloning to mimic the professional tone and cadence of a bank representative, making it difficult to distinguish a bot from a human employee.
Messages that create urgency
A hallmark of a scam is the creation of a time-sensitive emergency. These messages are designed to trigger an emotional response that bypasses your critical thinking.
- Security Alerts regarding account access restricted due to an unrecognized login in another state.
- Fraud Notifications asking if you authorized a $1,450.00 Zelle payment and telling you to reply NO to stop.
- Compliance Demands claiming your tax documentation is incomplete and you must update now to avoid account freezing.
Links to fake websites
The goal of the communication is to direct you to a phishing portal. Modern scammers use Adversary-in-the-Middle (AiTM) proxy sites. These are not just static clones; they act as a live bridge. When you enter your credentials into the fake site, the script passes them to the real Wells Fargo site instantly.
What happens after you respond
Once the scammer has a live session, the theft occurs within seconds.
- MFA Capture occurs when the fake site prompts you for your 2-Step Verification code. You enter it, thinking you are securing your account.
- Session Hijacking happens when the attacker captures the session cookie from the real bank. This gives them full access to the account as if they were you.
- The Sweep involves money being moved out via Zelle or ACH to mule accounts. Because these transactions are often authorized by the user under false pretenses, they can be difficult to reverse.
Common Wells Fargo Scam Examples
Scams are typically categorized by the medium they use, and understanding these patterns is key to identifying them.
Wells Fargo phishing email (account alert scams)
These are often disguised as official corporate communication or security updates. A recent real-world example involves an email stating New Security Document Available or Update to Your Account Disclosure. These emails usually contain an HTML or PDF attachment. Opening these can execute InfoStealer malware that scans your local browser for saved passwords and credit card data.
Wells Fargo text scam (smishing messages)
The wells fargo text scam is currently the most frequent threat because users tend to trust SMS more than email. You might receive a message from a random 10-digit number claiming your debit card has been deactivated. It almost always includes a shortened link that leads to a mobile-optimized fake login page designed to capture your PIN and CVV.
Phone scams impersonating fraud support
Vishing calls are the most high-pressure tactic. The caller ID may show Wells Fargo or a known bank number. The agent tells you your account is being hacked at that very moment and instructs you to move your money to a safe account or reverse a fake transaction by sending money to yourself via Zelle. In reality, you are sending money directly to the criminal.
Fake Wells Fargo login pages
These sites are the final destination for almost all phishing attempts. Always inspect the URL. A real site is wellsfargo.com, whereas a fake site might be wellsfargo-verify.net or use look-alike characters. These pages will ask for your username, password, ATM PIN, and even your Security Questions. Wells Fargo will never ask for your full PIN or password via an emailed or texted link.
Why These Scams Are So Convincing
Scammers have moved away from the obvious typos and broken formatting of the past. The primary reason these attacks succeed is the use of high-end technology to craft flawless professional language. Criminals now use templates that mimic the exact tone, font, and branding used by Wells Fargo corporate communications.
Another layer of deception is technical spoofing. Scammers use software to manipulate your phone caller ID, making it appear as if you are receiving a call or text from a legitimate Wells Fargo number like 1-800-869-3557. This creates immediate trust, leading many to believe they are speaking with an official fraud prevention agent.
When combined with personal data harvested from previous third-party breaches, such as your full name, address, or the last four digits of your social security number, the lure becomes nearly indistinguishable from reality.
Signs of a Wells Fargo Phishing Message
Even with advanced technology, there are specific behavioral markers that indicate a message is fraudulent. Wells Fargo follows strict regulatory protocols for customer contact that scammers cannot afford to follow if they want to steal your funds.
- Extreme Pressure and Threats involve messages claiming your account will be permanently deleted or that you will face legal action if you do not click a link within minutes. Legitimate bank alerts are informative and never use threats.
- Requests for Private Security Codes is the most critical red flag. Wells Fargo will never text or call you to ask for your Online Banking password, your ATM PIN, or a One-Time Access Code. These codes are for your use only to verify your identity on the official website or app.
- Unusual Redirects and Shortened URLs are common in fraudulent messages. Official communications typically direct you to sign on to the app or the main website. Scammers use shortened links like bit.ly or t.co to hide the final destination, which is usually a fake login portal.
- Instructions to Move Money are a definitive sign of a scam. Wells Fargo will never ask you to send money to yourself or any safe account via Zelle to reverse a fake transaction.
What to Do If You Receive a Suspicious Message
If you encounter a message that raises any red flags, your priority is to break the chain of communication immediately. Do not reply to a text message, even to say STOP, as this confirms to the scammer that your phone number is active and monitored.
For a suspicious email, do not click any links or download attachments like PDFs or HTML files. Instead, forward the entire email to reportphish@wellsfargo.com. Once forwarded, delete the email from your inbox and your trash folder.
If you receive a suspicious text, take a screenshot for your records and then forward the message to 7726 which is a service used by most US carriers to track and block fraudulent senders.
What to Do If You Already Clicked or Responded
If you have already entered your credentials into a fake site or shared a code over the phone you must act in seconds to mitigate the financial damage.
First call the Wells Fargo Fraud Department immediately. For personal accounts call 1-800-869-3557 and for compromised online profiles or suspicious Zelle transfers call 1-866-867-5568.
If you detect unauthorized credit card activity call 1-800-642-4720. Customers currently traveling outside the United States should use the official international access codes to find the specific toll free number for their current country.
Important Note: Do not use any number provided in a suspicious text or email. Only use official numbers found on the back of your physical debit card or the verified bank website. Inform the agent that your account has been compromised so they can freeze your cards and help you establish new login credentials.
Next log in to your official Wells Fargo account from a secure device and change your password. If you use the same password for other sites like your email or other banks, change those as well.
You should also place a fraud alert on your credit file by contacting one of the three major bureaus which are Equifax, Experian, or TransUnion. This prevents scammers from opening new lines of credit in your name using the data they harvested from the phishing attempt.
How Wells Fargo Protects Its Customers
Wells Fargo utilizes a multi-layered security stack to safeguard your assets. This includes 24/7 Fraud Monitoring where the bank’s systems analyze your spending patterns to detect anomalies. If a transaction seems out of character, the bank may automatically decline the purchase and send a legitimate alert to your verified mobile number or email.
The bank also offers Advanced Access which requires a secondary code for sensitive actions like adding a new Zelle recipient or changing your home address. Furthermore, your Wells Fargo debit and credit cards are covered by Zero Liability Protection. This means you are not held responsible for unauthorized transactions as long as you report them promptly.
To further harden your security, the bank encourages the use of biometric sign-on such as face or fingerprint recognition which is much harder for a remote scammer to spoof than a traditional password.
Conclusion
Protecting your wealth from fraudulent activity requires constant vigilance and a healthy skepticism of unsolicited contact. While scammers use advanced tools to mimic the bank’s appearance, their goal is always to bypass your logic using fear and urgency. By keeping your security codes private, verifying every link, and using the bank’s official contact channels, you can effectively neutralize even the most sophisticated phishing attempts.
For further details on how to report a suspicious email or website, you can visit the official reporting page at: https://www.wellsfargo.com/privacy-security/fraud/report/phish/
Reporting these incidents helps the security community track and shut down fraudulent domains before they can harm more people.
Frequently Asked Questions
Does Wells Fargo send text messages with links?
Wells Fargo may send you text alerts if you have enrolled in the service, but these typically ask you to log in to your official app or wellsfargo.com. Be extremely cautious of any text with a link that takes you directly to a login page, especially if the link uses a URL shortener.
How can I verify a Wells Fargo email?
The safest way to verify an email is to ignore the links inside it and log in directly to your account via the Wells Fargo Mobile app. Legitimate secure emails from the bank will often require you to log in to a Secure Messaging Center using credentials you have previously established.
Can scammers access my account without OTP?
While it is more difficult, scammers can use malware or session hijacking to bypass security. However, the vast majority of successful scams rely on the user voluntarily providing a One-Time Passcode during a social engineering call or on a fake website.
What should I do after clicking a phishing link?
If you clicked a link but did not enter data, run a full antivirus scan on your device to check for malware. If you did enter your login details, call 1-800-869-3557 immediately and change your online banking password from a different secure device.